I decided to search for penguin. According to the right hand side of Cuil, there are 66,229,028 results for penguin.

First of all, the website design is really nice. I know that doesn't matter as much, but I had to say that :-) I also like the columns, the short snippets and the pictures to the side. I have to agree with Cuil that showing a picture can help the user determine relevance (FAQ #7).
There's even some tabs and a pull down menu across the top of the search to help narrow down your interest, such as ``Penguin Books'', ``Penguin Classics'', ``Penguin Putnam'', ``Linux Penguin'' etc.. Ok, that's nice.
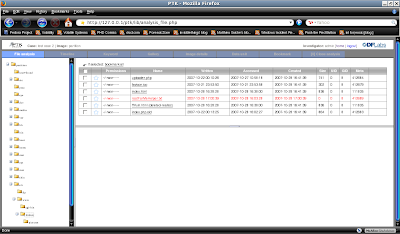
Now for the vanity searches. First off, I'm not some conceited schmuck who likes to google herself all the time, but I know what should pop up when my name is entered. Here it goes: there are 3,619,749 results for the search term ``jamie levy'' (without quotes).
Ok, so something of mine is not on the first page like on Google. Big deal. There's something of mine on the second page:
It's a tutorial of mine. It's kind of old, and it's kind of buried in my site... I thought I would at least see the index of my site if anything... Also, I'm not really sure what that picture is next to my page. I know I didn't put it there.
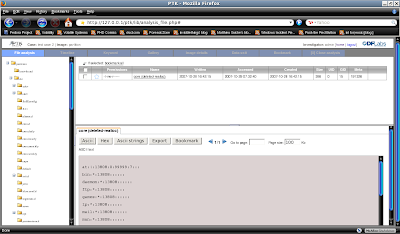
Ok, on the third page I see the same tutorial above as well as another OLD tuturial of mine that I forgot to take offline after I rewrote it. So that's bizarre, why would the first resulting tutorial repeat to the second page? What is that picture next to it? How did they find the old Unix tutorial?:
This seems to be a pattern, however as I found more repeats of these results and finally my index page on the fourth page of results. However, there is finally a correct picture next to the wireshark tutorial:
After looking just little bit more I found another old course page of mine, which repeats as well:

Ok, so what happens if I decide to narrow down my search and look for myself at the place where I work? Cuil only shows four results (though it claims there are 43,752 results), three of which we have already seen above. Look next to the Unix tutorial, do you find anything curious there? I did:
Who is that man in the picture? He's so mysterious.... I know I didn't put him there! Here's a closeup:

Bizarre is all I can say... Does his picture seem relevant to Unix? I wouldn't think so... but it seems like some of these pictures are just random. Also the stuff that Cuil pulls up seems as if it's from some older snapshot. I haven't quite figured it out.
Well, I won't bore you with details of other people I ``Cuil''ed, but I thought it was interesting that I couldn't find my past adviser at all when there are 815,000 pages in Google related to his name.
I guess he isn't ``Cuil'' enough... :-)